IT Managed Services

CISA Alert: Akira Ransomware – A Rising Threat to Critical Infrastructure
The Top Cybersecurity Challenges Facing SMBs in 2026
CISA and Partners Issue Advisory on Chinese State-Backed Cyber Espionage
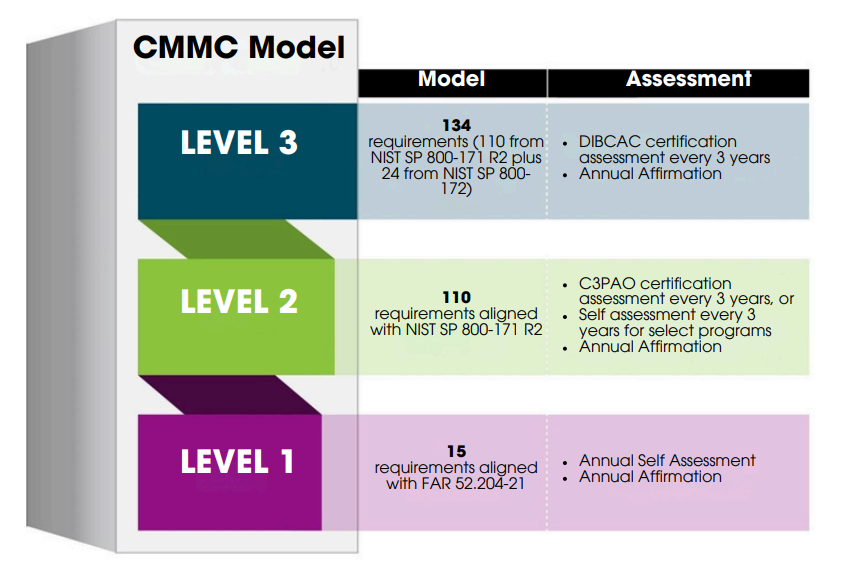
Rule 48 CFR: Where it Stands Now in the CMMC Rollout. What Defense Contractors Need to Know.
Cyber Insurance: A Must-Have for Small & Medium Businesses. What You Need to Know.
CISA Adds 3 Known Exploited Vulnerabilities. June 16, 2025: Apple, TP-Link Routers, and Linux Kernel
CISA and NSA Release Guide to Protect AI Data: May 28, 2025
CISA & ACSC Release Joint Advisory on SIEM & SOAR Implementation: May 29, 2025
Categories
- AI
- CISA Alerts
- Cloud Computing
- Cloud Infrastructure
- CMMC
- Compliance
- Critical Infrastructure
- Cybersecurity
- Cybersecurity Advisories
- Department of Defense
- Firmware
- Government
- IT Consulting
- IT Managed Services
- Managed IT
- Managed Service Provider
- Managed Services
- News
- Ransomware
- Recruiting
- Social Media
- Staffing
- Technology
- Uncategorized
- Vulnerability Management
Tags
AI Anti-Malware Anti-virus CISA CISA Alerts CMMC compliance Compliance as a service coronavirus covid19 critical infrastructure CSA cyberattacks cyber resilience cybersecurity Cyber Security Cybersecurity Advisories Cybersecurity Advisory cybersecurity threat detection cyber threats data breaches Desktop Support endpoint protection FBI firmware firmware attacks Firmware Compromise gap analysis healthcare incident response plans Information Technology IT consulting IT managed services Malicious Firmware malware Managed IT Services Managed Service Provider Managed Services managed services provider microsoft Microsoft Windows MSP multi-factor authentication Network Security NSA phishing ransomware recruiting routers Schneider Electric Siemens small and medium-sized businesses SMBs spam Spry Squared virus Vulnerability Vulnerability Management Vulnerability Management. critical infrastructure Windows 10