
New Search
Not happy with the results? Type your search again

The Cybersecurity Maturity Model Certification (CMMC) is a certification process created by the Department of Defense (DoD) that creates unified

What is a vCIO and What are the Benefits of a VCIO for my Business?
As your company grows so too does the complexity of your technology. In the beginning, your organization was able to survive by setting up your own computers, googling information,

What are Managed IT Services?
Which of these technology challenges have you experienced in the past 24 hours? In the past week? In the past

IT Strategy: What Is It, Why It’s Important, and How to Develop One
Typically, dealing with your company’s technology has been reactionary rather than proactive. What do we mean by this? In the

Cybersecurity Maturity Model Certification (CMMC) Guide
At the end of 2017 the Department of Defense (DoD) started to require organizations that were a part of the Defense

What is Compliance as a Service?
Businesses today handle large amounts of sensitive electronic data including client information, emails, payment details and employee information. Much of

Firmware: What it is and Why it is so Vulnerable to Hackers
Most companies pay close attention to the security of their computers, software, and hardware, but there is one piece of

Top 4 Cybersecurity Gaps of 2020
Just like Information Technology, cybersecurity threats are evolving every day. No matter how much changes, the most common cybersecurity gaps
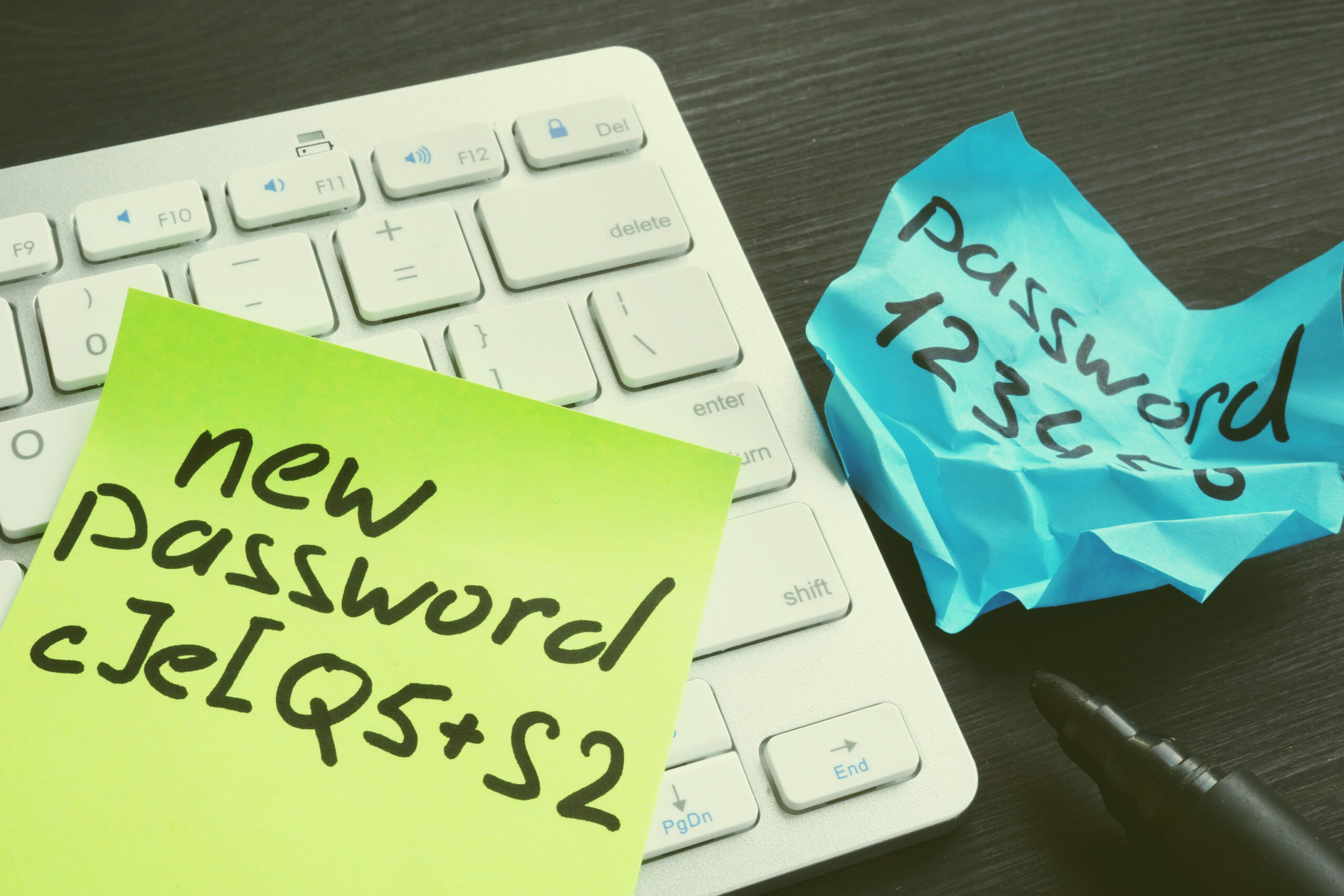
7 Tips for Password Management Best Practices
Password management is a major problem for businesses across the globe. Verizon’s 2020 Data Breach Investigation Report states that 81%

Why Use Outsourced Managed IT Services?
What are your options to manage your company’s technology? Companies currently delivering highly qualified professional and skilled personnel are reaching







